Nothing is more frustrating than finding out that your WordPress website is hacked. After all, your WordPress website is your hard work over many months or years and the last thing that you expect isn’t learning that your website is hacked. In order to prevent hackers from attacking your WordPress website, the first step is to know what are the possibilities and reasons for your WordPress website to get hacked. With a better understanding of these reasons, it will be easy for you to implement solutions for preventing the hacking attempts on your WordPress website.
Why Do Hackers Target WordPress?
Not just WordPress but all types of websites on the internet are vulnerable to hacking attempts. One of the main reasons why the WordPress websites are a common target for the hackers is because WordPress is the most popular website building platform. As WordPress is extremely popular and commonly used, hackers constantly try to find out websites that are less secure so they can breach into such websites. Hackers have different motives for hacking websites. Some of the hackers are beginners who are learning to analyze and get into the less secure websites; while some hackers have malicious intentions like injecting a website with Malware, making use of a website to attack other websites or performing spamming activities.
How A WordPress Site Gets Hacked?
It is important to understand how a WordPress site gets hacked.
Below are the types of WordPress security vulnerabilities that lead to hacking of your website:
Backdoors
With the backdoor vulnerability, hackers get secret passages that bypass security encryption for getting access to WordPress websites via irregular methods – wp-Admin, FTP, SFTP, etc. Once they get an access, hackers can cause disaster on hosting servers with the help of backdoors by cross-site contamination attacks – affecting multiple sites hosted on the same server. As per the Sucuri’s Q3 2017 report backdoors continue to be one of the many post-hack actions taken by the attackers, with 71% of the infected sites that have some form of backdoor injection.
Often, backdoors are encrypted in such a way that they appear like legitimate WordPress system files, and get an access to WordPress databases by taking the advantage of weaknesses and bugs in outdated versions of the platform.
A prime example of backdoor vulnerability, TimThumb fiasco exploited the old scripts and outdated software impacting millions of websites.
You can prevent the backdoor vulnerability by scanning your WordPress site with tools such as SiteCheck which easily detects the common backdoors. Additionally, you can also block IPs, enable two-factor authentication, restrict admin access and prevent unauthorized execution of PHP files easily to secure from this vulnerability.
Pharma Hacks
With Pharma Hack the hacker can insert rogue code in outdated versions of WordPress websites and plugins, due to which the search engines return ads for pharmaceutical products when an affected website is searched for. The vulnerability appears to be a spam instead of traditional malware. But the search engines get enough reason to block the site for distributing spam.
Pharma Hack includes backdoors in plugins and databases. However, the exploits are often in the form of encrypted malicious injections present in databases and require a detailed clean-up process to fix the vulnerability. Pharma
Hacks can be easily prevented by asking your WordPress hosting providers for updating the servers and regularly updating your WordPress installations, themes, and plugins. MilesWeb offers the automatic WordPress updates feature that keeps your WordPress always updated.
 Brute-force Login Attempts
Brute-force Login Attempts
In Brute-force login attempts, automated scripts are used for abusing weak passwords and gaining access to your site. Limiting login attempts, two-step authentication, blocking IPs, monitoring unauthorized logins and using strong passwords are some of the easiest and highly effective ways to avoid brute-force attacks. Though these security practices are easy to implement many WordPress website owners fail to perform these security practices.
Due to this, hackers are easily able to destroy as much as 30,000 websites in a single day via brute-force attacks.
 Malicious Redirects
Malicious Redirects
Using malicious redirects, backdoors are created in WordPress installations using SFTP, FTP, wp-admin, and other protocols, and redirection codes are injected into the website. Usually, the redirects are placed in your .htaccess file and other WordPress core files in encoded forms that direct the web traffic to malicious sites.
 Cross-Site Scripting (XSS)
Cross-Site Scripting (XSS)
Cross-Site Scripting (XSS) involves injecting a malicious script into a trusted website or application. This is used by the attacker to send malicious code, typically browser-side scripts, to the end user without letting them know about it. Usually, the intent is to grab cookie or session data or perhaps even rewrite HTML on a page.
WordFence states that Cross-Site Scripting vulnerabilities, commonly found vulnerability in WordPress plugins by a significant margin.
 Denial of Service
Denial of Service
And now this is the most dangerous of all, Denial of Service (DoS) vulnerability. This exploits errors and bugs in the code to overcome the memory of website operating systems. Hackers have threatened millions of websites and earned millions of dollars by abusing outdated and buggy versions of WordPress software with DoS attacks. Though small companies won’t be a target of financially motivated cybercriminals, they try to commit outdated vulnerable websites to create botnet chains for attacking large businesses.
Unfortunately, even the latest WordPess software versions can’t broadly fight against the high-profile DoS attacks, but will surely help you to avoid getting trapped in the fight between financial institutions and refined cybercriminals.
How to identify if your website has actually been hacked?
The worst thing happened, when you entered to your blog and tried to open it but you have a warning message saying that your site has been hacked. OMG. …… What to do now?
Of course, now you wonder how to recover the hacked WordPress site.
But the first thing that you should do is don’t panic, take deep breath and get relaxed and try to identify the problem.
First thing you have to do is to figure out whether your site has actually been hacked or not.
Yes, obviously it is the first thing you need to know.
There are plugins to detect whether your website was infected or not. For me one of the best tools to identify the WordPress infections is “Sucuri”. In addition, by using Sucuri WordPress plugin you will get alert messages every time when someone will try to attack on your website.
You can identify if your site is really hacked if you face the below situations:
- You aren’t able to log in.
- Your website home page is blank or displaying “You have been hacked” message.
- All content and pages has been removed from your site.
- You see unknown things like new content, advertisements, pornography materials on your website header and footer. For instance, you might see the homepage is replaced by a static page or new content is added to it.
- Website redirection to some other sources (spam websites).
- Your web host sending you emails about spam and other malicious activities.
- You search on Google “site:example.com” and getting indexed pages and content that looks malicious.
- While searching for your site, you or your users get a warning in your browser.
- When you search for your site in Google, it gives a warning that your site may have been hacked.
- You get a notification from your security plugin about a breach or an unexpected change.
Now you are sure that you have actually been hacked. So what next thing you can do to get your WordPress website back.
Top 10 Reasons Why Your WordPress Website Can Get Hacked And How To Prevent Them?
Below are the top 10 reasons why your WordPress website can get hacked:
Let’s have a look at some of the top reasons why a WordPress website can get hacked:
#1 Insecure Web Hosting Platform
It is extremely important to research about the WordPress hosting platform before signing up for one. Some hosting companies do not secure their web hosting platforms completely. As a result of this, all the websites hosted on their server are vulnerable to the hacking attempts and malicious activities. This can be avoided by choosing a secure WordPress hosting platform. At MilesWeb, WordPress hosting is fast, easy and highly secure.
With every WordPress hosting package, MilesWeb also provides services like server caching, cloning, CDN, Railgun and daily backups. Share on XThis WordPress hosting platform is crafted for high-performance and faster page load speed. All the WordPress hosting packages at MilesWeb are backed by the latest Intel Xeon processors that help in making your website fast, efficient and completely secured.
#2 Use Of Weak Passwords
Your admin password is the key to your WordPress website. It is highly important to use a strong and unique password for every account mentioned below as a hacker can breach into your website if he gets access to these accounts:
- Web hosting control panel account
- WordPress admin account
- MySQL databases used for your WordPress website
- FTP accounts
- Email accounts used for the WordPress account
All the accounts mentioned above are protected through passwords. If you use weak passwords, it becomes very easy for the hackers to get to your password with some hacking tools. You can avoid this with the use of strong and complicated passwords that are not easy to guess.
#3 Using ‘Admin’ As The WordPress Username
You must refrain from using ‘Admin’ as your WordPress username. If the username of your WordPress admin account is ‘Admin’, then change it to a different username right away because hackers look for the admin username to breach into your account. If you change your admin username to something else, the hackers would not easily know that this is your admin account. You can share the login credentials of the admin username to the clients and users on the website if you wish to.
#4 Unprotected Access To The WordPress Admin Area
You can perform various functions on your website through the WordPress admin area. This is the most commonly attacked part of the WordPress website. If your WordPress admin area is unprotected, hackers can crack your website by trying various methods. You can restrict the hackers by adding various layers of authentication to get to your WordPress admin directory.
Your first step is to password protect the WordPress admin area. This adds an additional layer of security and anyone who tries to access your WordPress admin account will have to provide the password. If your WordPress website consists of various authors and users, then it is preferable to use strong passwords for all the user accounts.
You can also make use of two factor authentication so that it is not easily possible for the hackers to get into your admin area.
 #5 Incorrect File Permissions
#5 Incorrect File Permissions
File permissions are basically a set of rules used by the web server. These permissions support the web server in terms of managing access to files on your website. If the file permissions are incorrect, a hacker can get access to write and change the files. It is important to ensure that all your WordPress files must have 644 value as the file permission and all the folders on your WordPress website must have 755 as the file permission.
#6 WordPress Version Not Updated
Some WordPress users do not update the WordPress version in time; at times they feel that by doing so their WordPress website might become slow or might be affected adversely. But that’s not right, when you see a new update for WordPress you must implement it immediately because every new version of WordPress fixes the bugs and security vulnerabilities that were present in the earlier version. Updating the WordPress version is simple yet a very effective way of protecting your website.
In case you are afraid that you might lose some data while updating the WordPress website, then you can create the complete website backup first and then update the website. Thereby, if something goes wrong or if something doesn’t work, then you will not lose any data and you can easily get back to the previous WordPress version.
Related : 7 Excellent WordPress Backup Plugins For Easy Website Backup
#7 WordPress Plugins And Themes Not Updated
Just like it is important to update the WordPress version, it is also important to update the plugins and the theme that you are using. If any of your plugin or theme is outdated, then your website becomes vulnerable to hacking attacks. Security defects and bugs are often found in WordPress plugins and themes. Usually, the owners of the plugins and themes fix them immediately, but if the user does not update the theme or plugin, then the website becomes vulnerable. Therefore, it is important to ensure that all your plugins and themes are updated.
#8 Use Of FTP In Place Of SFTP / SSH
The FTP accounts are used for uploading files to the web server through an FTP client. Most of the hosting providers support the FTP connections with various protocols, you can connect with plain FTP, SFTP or SSH.
When you connect to your WordPress website through plain FTP, the password that you enter is sent to the web server unprotected and unencrypted. Hackers might spy on your FTP connection and your password might be easily detected and stolen. Therefore, in place of using FTP, you can make use of the SFTP or SSH connections.
For using the SFTP or SSH connection, there is no need for you to change the FTP client. Most of the FTP clients can connect to your website through SFTP and through SSH as well. For this, all you have to do is change the protocol to ‘SFTP – SSH’ while connecting to your website.
#9 Nulled Themes & Plugins
You will come across many websites on the net that offer paid WordPress plugins and themes for free. You might easily get allured for downloading and using these plugins and themes. If you download WordPress plugins and themes from unreliable sources, this can have dangerous negative effects on your website. These null plugins and themes can compromise the security of your website and they can also steal sensitive and important information from your website.
There is no harm in having many plugins and themes but you must ensure that you are downloading them through reliable sources. If any plugin or theme you like is a premium one, you can find many other free alternatives to it as WordPress has a wide range of plugins and themes available.
Related : Most Essential WordPress Plugins For Blogs And Websites
 #10 WordPress Configuration wp-config.php File Not Secured
#10 WordPress Configuration wp-config.php File Not Secured
The WordPress configuration file : wp-config.php consists of all your WordPress database login credentials. In case this file is compromised, then it will give out information that will make it easier for a hacker to get complete access and control over your website. You can add an additional level of protection to deny access to the wp-config.php file with the use of .htaccess. All you have to do is add the code mentioned below to your .htaccess file.
<files wp-config.php> order allow,deny deny from all </files>
The above mentioned reasons are the most common for your WordPress site to get hacked. So, make sure you remember them.
Steps to Recover a Hacked WordPress Website
Obviously, these measures are not simple and require some technical knowledge, and access out of the ordinary to your WordPress.
You have to use the following tools:
- FTP access to your server, or a file manager such as cPanel.
- Advanced text editor, type Notepad ++ or similar. You better really editor ordinary text, but one of these is easier to view the code.
Step 1: Put Your Site in Maintenance Mode
As soon as you find that your WordPress is infected, you have to throw down it to prevent hackers from abusing more. There is no way to clean up a website that is online. So, put your website in maintenance mode, work with files, and database quietly.
Follow these steps to get your site in maintenance mode without losing SEO positioning.
In this step, we will create a file in the root of your public folder on the server. Usually it is the same where the wp-includes, wp-admin or wp-content folders reside.
Create a Web page of “maintenance mode,” which 503.php going to call, and carry the following code:

Here you are telling the search engines that you are temporarily out of service, so you will be safe from penalties.
Step 2: Backup of Your WordPress
Even if your site could be infected, it is very important to have a backup in case things go from bad to worse. Obtain a complete backup of your website, including all databases. Download files and perform a full export via phpMyAdmin SQL.
If you have your site hosted on a hosting with cPanel, simply enter in your PhpMyAdmin and export the database and generate a zip with all the files in your WordPress folder. It is also a good idea to create a full backup of all that you have in your hosting.
An alternative that works very well and you will streamline this step, you can use the WordPress plugin ” BackupBuddy. ” IMPORTANT: Do not omit this step.
Step 3. Change All Passwords and Access
Before you start cleaning your room, go to the WordPress control panel and change the access credentials (for all users), do the same with passwords databases and restores WordPress secret keys found in the file “wp-config.php”. Click here to get secret Keys .
You can also change passwords though FTP.
Open wp-config.php file through FTP or the file manager, and locate the section where the database is configured.
Replace the MySQL user’s password in this file. You can change MySQL user’s password by logging into your cPanel >> MySQL.
Step 4: Change the Authentication Keys
WordPress uses different authentication keys to encrypt the stored information in session cookies; it makes your site more difficult to hack.
In addition to change the cookies, we will invalidate any session that is already open. You can create new keys by using the official WordPress key generator . You have to open your wp-config.php file to locate where these keys are, and replace them with the new generated keys.
Step 5: Scan Files and Folders
Once you change MySQL and WordPress passwords, it is recommended to scan the files and folders. You may ask your WordPress hosting provider to scan the files and folders using Maldet and Clamscan utilities.
If you find any plugins and themes with malicious files, it is recommended to remove such plugins and vulnerable files and use the alternative option. Even if you reinstall the plugins and themes, it might again get compromised as many plugins and themes have known backdoor.
If there are any plugins and themes which you do not require, make sure you remove them directly.
Step 6: Use Google Webmaster Tools
In recent years, Google has taken the initiative to identify and point out sites that have experienced a security compromise. If you have not checked your site status, then sign in Google Webmaster Tools and check if there are any warnings. You can scan your site by using google webmaster tools.
In Google Webmaster Tools, go to the domain you want to check, and click on “Problems of Security”. You have a breakdown of what Google has indexed and will find all the details and warning messages (if something is there).
Go to this link and scans your web to see what malicious files detected https://www.google.com/transparencyreport/safebrowsing/diagnostic/index.html#url
You can see where the malware is hosted, find all the infected files and delete them.
Finally
Send request to Google that you have made changes on your website and removed all malicious codes and infected files through Google Webmaster Tools.
Wait… its not over yet.
Now the time is to be prepared for future attacks. Do you want to be?
Protect Your WordPress Website From Hackers With These 25 Tips
Below are some tried, tested and efficient ways to protect your WordPress site:
Secure Your Login Page and Avoid Brute Force Attacks
Being a WordPress user, you know that the platform has a standard login page URL. The backend of the website is accessible from there and so, hackers try to brute force their way in. Simply adding /wp-login.php or /wp-admin/ at the end of your domain name will make it for you.
Below are the important things to be considered to secure your login:
1. Changing your login and password
Many WordPress users select “admin” as their default WordPress login username and this is very well known by hackers. Your login should be changed to something else that would confuse a hacker when trying to guess it. The username must comprise of some irrelevant name or something out of the blue but yes ensure that you remember it.
Next is the password which should contain lower case as well as upper case letters, numbers and symbols too. For example: your password should be like “iwbgfMT23$$”. You can make such combinations of the passwords and change them regularly.
For creating a strong password, you can follow a technique mentioned here. Take a sentence that you would recall, if you set it as a password. Pick the initials of the words in that sentence and add some digits and symbols to it. This type of password is almost very hard to be guessed as it would be meaningless.
2. Set up website lock-down and ban users
Have you heard about website lockdown feature? This can help solve a big problem by giving failed login attempts to the outsiders. When the hacker tries to access the site with repetitive wrong passwords, site will get locked and you will be notified of this unauthorized activity.
The iThemes Security plugin offers you the feature of failed login attempts and blocks the attacker’s IP address when the hacker tries to attempt to enter your website.
3. Use 2-factor authentication
Adding the 2-factor authentication (2FA) while logging into a website, is another security measure which is being applied by many websites today. This means the user provides login details for two different components. It depends on the website owner what those two factors would be. Those can be a regular password followed by a secret question, a secret code, a set of characters, etc.
4. Rename your login URL
Changing the login URL is an easy thing to do. The WordPress login page, by default, is easily accessible via wp-login.php or wp-admin added to the site’s main URL.
If the direct URL of your login page is known to the hackers, it is very easy for them to enter your website with a brute force attack. They try to log in with their Guess Work Database (also called as GWDb which is a database of guessed usernames and passwords; e.g. username: admin and password: p@ssword … with millions of such combinations).
This is a small trick that restricts an unauthorized user to access the login page. Only someone who knows the exact URL can do it. You can change the URLs as shown in below examples:
- Change wp-login.php to something unique; e.g. my_new_login
- Change /wp-admin/ to something unique; e.g. my_new_admin
- Change /wp-login.php?action=register to something unique; e.g. my_new_registration
5. Use email as login
You need to input your username to log in by default. Instead of using a username, you can use an email ID for a more secure approach. This is because usernames can be easily predicted while email IDs can’t be. Additionally, any WordPress user account is always created with a unique email address which makes it a valid indicator for getting logged in.
You can use the WP Email Login plugin for this as it starts working immediately after activation and there isn’t any configuration required at all.
For taking a test, you need to simply log out of your website and then log in again but this time you need to use the email address that you used for creating the account.
Secure your admin dashboard
The admin dashboard is the most interesting part for a hacker and the most secured section of all. It is quite challenging part for attacking the admin section but if the hackers succeed, it gives them a moral victory and access to exploit several things.
Here’s what you can do:
6. Protect the wp-admin directory
The wp-admin directory serves as the heart of any WordPress website. In case, this part of your site gets violated then the complete site might get damaged.
You can prevent this by password protecting the wp-admin directory. This type of security measure will allow the website owner to access the dashboard only after submitting two passwords. One is for securing the login page while the other secures the WordPress admin area. If the website users need to get access to only particular parts of the wp-admin, you may unlock those parts when you lock the rest.
The AskApache Password Protect plugin can be used for securing the admin area. An .htpasswd file is automatically generated; the password is encrypted as well as the correct security-enhanced file permissions are configured.
7. Use SSL to encrypt data
Another smart trick to protect the admin panel is to implement an SSL (Secure Socket Layer) certificate. With SSL you can ensure that your data is transferred in a secure way between the user browsers and the server which makes it difficult for hackers to breach the connection or spoof your info.
You can get an SSL certificate for your WordPress website easily, just by purchasing from some dedicated companies or asking for your web host to provide you with one (you will often find an option for SSL with the hosting packages).
Don’t forget that the SSL certificate also has a great impact on your website’s rankings in Google. The websites that are SSL certified rank higher in Google, as compared to those that aren’t. This ultimately means that there’s no more traffic. Do you want this to happen? Therefore, understand the importance of SSL to encrypt data.
Related: SSL Certificate Can Act Like A Superman To Protect Your Website
8. Add user accounts with care
In case, you are running a WordPress blog or a multi-author blog then you might be dealing with multiple people that access your admin panel. Due to this, your website can be highly vulnerable to security threats.
For this, installing a plugin like Force Strong Passwords might help your users for ensuring that the passwords they use are secure or not.
9. Change the admin username
While installing WordPress, don’t choose the username as “admin” for your main administrator account. This is very easily guessed by the hackers and they just need to know the password after this, leading to destruction of your website.
These types of attempts can be stopped with the use of the iThemes Security plugin that cleverly bans any IP address immediately as it tries to attempts to login with the “admin” username.
10. Monitor your files
For additional security, use plugins such as Wordfence, or again, iThemes Security that monitor the changes to the files of the website.
Secure the database
The site’s data and information is stored in the database and so, it is important to protect it. Below are the ways in which you can secure it:
11. Change the WordPress database table prefix
In case you have installed WordPress, you might be aware of the wp- table prefix used by the WordPress database.
You need to change it to something unique.
Your database becomes highly vulnerable to SQL injection attacks with this default prefix. You can prevent such attack simply by changing wp- to some other term, for example, you can make it mywp-, wpnew-, etc. You can take the help of plugins such as WP-DBManager or iThemes Security for this.
12. Back up your site regularly
Though you think your website is secure with all the essentials but it’s always better to improve. So, it’s always better to keep an off-site backup of your website saved somewhere.
When you have a backup, it can help you restore your WordPress website to a working state at any time you require.
There are some plugins such as VaultPress, BackupBuddy, BlogVault, CodeGuard, UpdraftPlus, etc. that can help you in taking backup of your WordPress website and restore it when required.
Related: 7 Excellent WordPress Backup Plugins For Easy Website Backup
13. Set strong passwords for your database
Even your main database user needs to have a strong password. It is the one that WordPress uses for accessing the database.
As recommended above, use combination of uppercase, lowercase, numbers, and special characters for the password.
14. Check your ‘comments’ and forms settings
When you enable comments on your posts, it is important to check your ‘Discussion’ settings. Ensure that all the comments are approved manually. It would add more administration work from your side but it’s always the best way for ensuring that no spam comments are entered.
Also, don’t miss to check that akismet is activated and that a Captcha is enabled on all your contact forms.
Secure your hosting setup
Almost all the hosting companies commit to offer an optimized environment for WordPress, but we can take a step further:
Related: Understanding Managed WordPress Hosting and When do you need one?
15. Protect the wp-config.php file
Crucial information about your WordPress installation is stored in the wp-config.php file which is the most important file in the root directory of your site. Securing it means securing the heart of your WordPress website.
If the wp-config.php file isn’t accessible to the hackers then they can’t breach the security of your site.
The good point here is that this can be done very easily. You simply need to take your wp-config.php file and place it to a higher level than your root directory.
If you store it to some other place, how can the server access it? The configuration file settings in the current WordPress architecture are set to the highest priority. So, though the file is stored one fold above the root directory, it is still visible to WordPress.
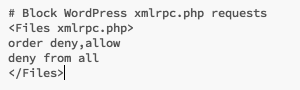
16. Protect xmlrpc.php (optional but recommended)
Only protecting the wp-config file isn’t enough. You also need to protect xmlrpc.php file as hackers commonly use it to hack a WordPress website. This file helps in remote communication with WordPress.
The use of xmlrpc (it is enabled by default from the WordPress version 3.8) can also be done to execute DDoS (Distributed Denial of Service Attacks) which can have a big impact on your website.
In case, you use the services such as JetPack, the official mobile wordpress app, pingbacks & trackbacks then only the XMLRPC is needed to be enabled.
For securing your xmlrpc.php file add the below code to your .htaccess:
17. Secure your .htaccess
Only tweaking your wp-config.php for security isn’t enough, you also need to secure your .htaccess file. Hackers can easily delete the code securing the wp-config.php file making your WordPress site vulnerable to attacks.
You should consider protecting your .htaccess file as one of the top priorities. You can do this by adding a code in the root .htaccess file of your domain:
<Files ~ “^.*\.([Hh][Tt][Aa])”> Order allow,deny deny from all satisfy all </Files>
18. Secure your .htaccess
The wp-admin file comprises of sensitive data and needs to be accessed only by the owners. You can prevent other users from accessing this file by using .htaccess.
You can add the following code by opening the .htaccess file present in the wp-admin folder:
#deny access to wp admin order deny,allow Allow from xx.xx.xx.xx # This is your static IP deny from all
This code restricts all the users other than those using the “xx.xx.xx.xx” IP (your static IP) from accessing the files in wp-admin.
19. Disallow file editing
The users those have admin access to your WordPress dashboard can easily edit any files that are a part of WordPress installation. These files include all the themes and plugins.
But, if you restrict file editing, a hacker too wont’ be able to modify any file even if he gets the admin access to your WordPress dashboard.
Add the following command to the wp-config.php file (at the very end):
define('DISALLOW_FILE_EDIT', true);
20. Connect the server correctly
It is recommended to connect the server only via SFTP or SSH while setting up your site. Since SFTP offers more security features as compared to the traditional FTP which aren’t included in FTP.
The server when connected in this manner ensures that the files are transferred securely. This service is offered by many hosting providers as a part of their package. In case it’s not, it can be done manually.
21. Set directory permissions carefully
If you set wrong directory permissions, it can prove to be fatal, especially in a shared hosting environment.
In this case, it is better to change the files and directory permissions for securing the website at the hosting level. Set the directory permissions to “755” and files to “644” for protecting the complete file system – directories, sub-directories, and other files.
This is done manually through the Files Manager inside your hosting control panel or via the terminal (connected with SSH) by using the “chmod” command.
In case, you create a new directory as a part of your website and don’t include an index.html file in it, your visitors can get the complete directory listing of everything that is in that directory.
For example, if a directory called “data” is created, you can see everything in that directory simply by typing http://www.example.com/data/ in your browser. There’s no need of password or anything.
This can be prevented simply by adding the below line of code in your .htaccess file:
Options All –Indexes
Secure your WordPress themes and plugins
Any WordPress site comprises of themes and plugins as essential ingredients. But it’s quite unfortunate that they can pose serious security threats. Let’s check the ways in which WordPress themes and plugins can be secured:
Related: Top 20 WordPress Plugins for E-commerce Website
23. Update regularly
Developers support every good software product and also it gets updated regularly, but WordPress gets updated very frequently. These updates are done for fixing the bugs and sometimes contain vital security patches.
If you don’t update your themes and plugins, you can be in a serious trouble. Don’t forget that many hackers rely on the fact that people are least bothered to update their themes and plugins. Often, these hackers exploit bugs that are already fixed.
So, it’s always recommended to update the WordPress products regularly.
24. Update your WordPress version
Make it a point to update your WordPress site to the latest version. Each time when you see there’s an update available, it means that the WordPress team has already added the security patches.
Similar to all the reputed software products even WordPress is supported by its developers and gets updated quite frequently. These updates are actually the fixes for bugs and also contain vital security patches sometimes.
If you don’t update your themes and plugins, you can face serious trouble. This is because several hackers know that people don’t care much about updating their plugins and themes. Therefore, hackers exploit the bugs that already have been fixed.
This means it is very important to update your WordPress products regularly – plugins, themes and everything.
25. Remove your WordPress version number
It’s very easy to find the current WordPress version. It is basically placed in the site’s source view.
This indicates that if the hackers know which version of WordPress is being used by you, it is very easy for them to plan the perfect attack.
It is possible to hide your version number with any security plugin mentioned earlier.
Conclusion
For a beginner, there’s a lot to be taken from this article. It is because it includes everything right from the reasons for website to get hacked, points to identify if your site is really hacked as well as the steps to follow after the site gets hacked and also the tips to secure your website from hackers in future. The more you care about your WordPress website security, the harder it will be for a hacker to break in. It is important to take some protective measure to secure your WordPress website from hackers. You simply need to follow the above mentioned guidelines for your website security. Hackers can cause big losses to your website or business. So, always remember prevention is better than cure.
Are looking for managed WordPress hosting? You have landed at the right place. Just at $1/mo get managed WordPress hosting to start your online business today itself.